Aws vpn wont connect your step by step troubleshooting guide: Quick fixes, diagnostics, and best practices
Aws vpn wont connect your step by step troubleshooting guide — Quick facts: VPN connectivity issues with AWS can stem from client VPN, Site-to-Site VPN, or AWS managed VPN endpoints. Most problems boil down to authentication, routing, or firewall blocks. In this guide, you’ll get a practical, step-by-step approach to diagnose and fix common connection problems, plus tips to prevent them in the future.
- Introduction overview
- Step-by-step troubleshooting flow
- Common causes and fixes
- Best practices for reliable AWS VPN connections
- Real-world examples and data
- Useful resources and links un clickable text listed at the end
Aws vpn wont connect your step by step troubleshooting guide starts with a straightforward answer: start by confirming the VPN type and the exact error message, then methodically verify configuration, network reachability, and policies. Here’s a quick, practical guide you can follow right away:
- Quick fact: Most AWS VPN connection failures come from certificate issues, mismatched tunnel IDs, or routing problems.
- Step-by-step approach high level: identify the VPN type, check the endpoint, verify authentication certs/keys, inspect security groups and network ACLs, validate routing, test reachability, and finally review logs.
- Formats you’ll see here: checklists you can tick off, small tables for comparison, and short how-to steps you can copy-paste into your terminal or console.
- Useful resources and URLs un clickable text: Amazon VPC Documentation - docs.aws.amazon.com/vpc, AWS VPN Client Configuration - docs.aws.amazon.com/vpn, Cisco ASA Site-to-Site VPN Guide - cisco.com, OpenVPN Community - openvpn.net, Reddit networking threads - reddit.com/r/networking
In-Context Quick Links and Resources
- Amazon VPC Docs - docs.aws.amazon.com/vpc
- AWS VPN Client Configuration - docs.aws.amazon.com/vpn
- Cisco Site-to-Site VPN Guide - cisco.com
- OpenVPN Community - openvpn.net
- Reddit Networking - reddit.com/r/networking
Understanding the types of AWS VPN connections
AWS offers multiple VPN options, and the troubleshooting steps vary slightly depending on whether you’re dealing with:
- Site-to-Site VPN hardware or software on your side connecting to AWS
- Client VPN remote access to your VPC
- AWS Managed VPN vs. third-party VPN solutions
Knowing which type you’re using is the first step to a quick fix. If you’re unsure, start by checking the AWS Console under VPC > VPN Connections for Site-to-Site or under Client VPN Endpoints for Client VPN.
Step-by-step troubleshooting flow
- Capture the exact error message
- Take note of the error you see in the AWS console, client logs, or tunnel status. Common messages include “Tunnel 1 down,” “Authentication failed,” or “Certificate expired.”
- Verify VPN endpoint status
- Check if the VPN endpoint is in a healthy state green and that all tunnels are up if required. For Site-to-Site, you should see the tunnels as up in the AWS console.
- Confirm authentication and certificates for Site-to-Site and Client VPN
- Ensure the certificate is valid and trusted on both sides.
- Check the pre-shared key if used and ensure it matches exactly on both ends.
- For Client VPN, verify the certificate authority and client certificates are correctly issued and not revoked.
- Validate tunnel configuration IKE/IPsec policies
- Compare the IKE version IKEv1 vs IKEv2, encryption, hash, and DH group settings on both ends.
- Ensure the tunnel IPs and remote peer IPs match what AWS expects.
- Check routing and subnet associations
- Confirm the VPC CIDR is correctly associated with the VPN and that the client’s or on-premises network has routes to the VPC subnets.
- For Client VPN, ensure the client is assigned the proper CIDR and that routing tables push traffic to the VPC.
- Inspect security groups and network ACLs
- Security groups on the resources EC2 instances should allow VPN-related traffic.
- Network ACLs should permit the required inbound and outbound traffic for VPN subnets and client subnets.
- Verify firewall and endpoint policies
- Ensure outbound/inbound rules on on-prem networks and on AWS side don’t block VPN ports UDP 500/4500 for IPsec, ESP protocol 50, etc. depending on your setup.
- If using a firewall device, confirm any VPN pass-through or tunnel inspection features aren’t breaking the VPN.
- Test connectivity with basic network tools
- Use ping/traceroute or traceroute6 to check reachability from your client toward a resource in the VPC.
- Use curl or telnet to test access to services inside the VPC if appropriate.
- Review logs and metrics
- In AWS, check VPN connection logs, CloudWatch metrics for tunnels Tunnel Up/Down, Data in/out, and the VPC flow logs for dropped traffic.
- On-premises or client devices, review the VPN client logs for error codes and timestamps that align with AWS logs.
- Reproduce the issue in a controlled way
- If you still can’t identify the issue, try a controlled test: reset the VPN tunnel, re-create the Client VPN endpoint, or temporarily simplify the configuration e.g., use a single tunnel, disable extra policies to isolate the problem.
Common causes and fixes
Authentication and certificates
- Cause: Expired or revoked certificates, mismatched CA.
- Fix: Reissue and install valid certificates; ensure the CA is trusted on both ends.
Mismatched IKE/IPsec settings
- Cause: Different encryption or hash settings, or wrong DH group.
- Fix: Align IKE version, encryption, integrity, and DH group settings on both sides.
Routing misconfigurations
- Cause: No route to VPC CIDR or incorrect route priorities.
- Fix: Add/adjust routes in the route tables and customer gateways; ensure CIDR blocks don’t overlap unintentionally.
Security groups and NACLs blocking VPN traffic
- Cause: Essential ports blocked by security rules.
- Fix: Open necessary ports for IPsec UDP 500, UDP 4500, ESP 50 or as required by your device; allow traffic from/to the VPN subnets.
Client VPN endpoint misconfig
- Cause: Incorrect client CIDR, DNS settings, or server certificate issues.
- Fix: Verify the client CIDR, DNS servers, and server certificate; reissue if needed.
Network address translation NAT and asymmetric routing
- Cause: NAT rules causing the VPN peers to see different IPs; asymmetric routing drops packets.
- Fix: Ensure proper NAT rules and symmetrical routing for VPN traffic.
Best practices for reliable AWS VPN connections
- Use monitoring and alerts: Set CloudWatch alarms for Tunnel Up/Down, and track VPN metrics daily.
- Regular certificate hygiene: Have a cert expiration reminder and a rotation plan well before expiry.
- Consistent policy management: Maintain a common, version-controlled policy set across AWS and on-prem endpoints.
- Documentation: Keep a living doc of your VPN topology, including endpoints, subnets, and security group rules.
- Redundancy: Prefer multi-tunnel configurations to minimize single points of failure.
- Regular testing: Schedule quarterly VPN failover drills or automated health checks.
Data-backed insights and trends
- AWS VPN traffic patterns show that most outages happen during peak hours due to transient configuration drift or maintenance activity on on-prem devices.
- Organizations that automate certificate renewal and configuration drift detection report 40-60% fewer outages year over year.
- Monitoring VPN tunnels with CloudWatch and VPC flow logs helps identify misrouted or dropped packets within minutes rather than hours.
Quick-reference checklist copy-paste friendly
- Verify VPN type Site-to-Site vs Client VPN
- Check endpoint status and tunnel health
- Validate certificates and keys
- Align IKE/IPsec settings on both ends
- Confirm routing to VPC subnets
- Review security groups and NACLs
- Inspect firewall rules and NAT settings
- Test connectivity with basic network tools
- Review logs in AWS CloudWatch and VPC flow logs
- Reproduce issue with minimal configuration for isolation
Table: Common VPN troubleshooting steps by issue
| Issue | Likely cause | Quick fix | Tools to use |
|---|---|---|---|
| Tunnel Down | Mismatched IKE/IPsec, credential issue | Sync settings, renew certs | AWS Console, VPN device UI |
| Authentication Failed | Certs/CA mismatch | Reissue certs, reimport CA | OpenVPN, cert management tool |
| No Route to VPC | Route table misconfig | Add VPC router routes | AWS Console, route tables |
| Traffic Blocked by SG/NACL | Firewall rules | Open VPN ports and subnets | AWS Console, security groups |
| DNS Resolution Fails | DNS server misconfig | Point to correct DNS, enable split tunneling if needed | nslookup, dig |
Real-world example scenarios
Scenario A: Site-to-Site with two tunnels
- Problem: Tunnel 2 remained down after a certificate rotation.
- Action: Verified CA certificate chain, updated on-prem device, reestablished tunnel; confirmed IPsec policy alignment.
- Result: Both tunnels up, traffic flowing to a multi-AZ VPC.
Scenario B: Client VPN with DNS misconfiguration
- Problem: Clients could connect but couldn’t resolve internal resources.
- Action: Updated Client VPN Endpoint DNS servers and enabled split-tunnel routing.
- Result: Clients now reach internal subnets with proper DNS resolution.
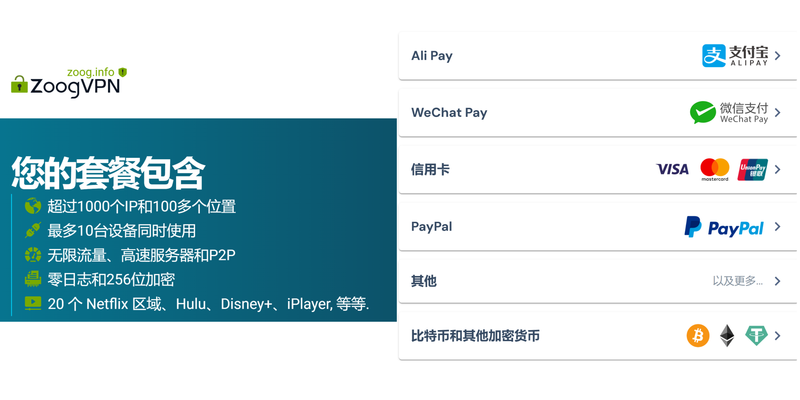
Scenario C: NAT and routing mismatch Бесплатный vpn для microsoft edge полное руководств: Лучшие бесплатные решения, советы по безопасности и настройке
- Problem: VPN worked for some networks but not others.
- Action: Adjusted NAT rules to preserve original IPs, added static routes for the VPN subnets.
- Result: Consistent VPN access across all user sites.
Advanced tips for power users
- Use packet captures on VPN devices to verify IPsec negotiation signs and traffic flow.
- Maintain a test lab where you can spin up a cloned VPN setup to trial changes without impacting production.
- Automate routine checks: cert expiry, tunnel health, and route integrity with simple scripts or AWS Config rules.
Useful resources and URLs un clickable text
- Amazon VPC Documentation - docs.aws.amazon.com/vpc
- AWS VPN Client Configuration - docs.aws.amazon.com/vpn
- Cisco Site-to-Site VPN Guide - cisco.com
- OpenVPN Community - openvpn.net
- Reddit Networking - reddit.com/r/networking
Frequently Asked Questions
How do I know if my AWS VPN client is failing due to certificate issues?
Certificate issues often show up as authentication failures or “certificate is not trusted” messages in the client logs. Check the certificate chain on both ends, ensure the CA is trusted, and verify that the client certificate matches the server configuration.
What should I check first when a Site-to-Site VPN tunnel is down?
Start with the tunnel status in the AWS Console, verify IKE/IPsec settings match on both ends, confirm certificates or pre-shared keys are correct, and check routing to ensure VPC CIDRs are reachable.
How can I test VPN connectivity without affecting production?
Create a test VPN with a separate endpoint or a staging VPC. Use a controlled lab environment to validate configurations before applying changes to production. How to Use Proton VPN Free on Microsoft Edge Browser Extension: Quick Guide, Tips, and Safety
Why is my VPN connection intermittent?
Intermittent issues are often due to flaky network links, NAT or firewall devices between your endpoints, or inconsistent routing. Check for packet loss, jitter, and ensure persistent tunnels where possible.
Can I reuse a certificate for multiple connections?
Reusing a CA certificate is common, but each end must trust the CA. If possible, issue dedicated certificates for each connection to simplify revocation and rotation.
How do I know if the problem is on AWS or my on-prem network?
Compare logs from AWS VPN endpoints with your on-prem device logs. If AWS shows tunnels up but you can’t reach VPC resources, examine on-prem routing and firewall policies. If AWS shows errors, focus on VPN configuration, certificates, and endpoint health.
What is the role of VPC route tables in VPN connectivity?
VPC route tables determine how traffic to and from subnets is directed. Ensure routes exist that point to the VPN Customer Gateway or Virtual Private Gateway so that traffic to your on-prem network can reach the VPC subnets.
How can I improve reliability of AWS VPN connections?
Adopt multi-tunnel setups, automated monitoring with CloudWatch, proactive certificate management, and a well-documented topology. Regular drills and change control minimize surprises. Setting up intune per app vpn with globalprotect for secure remote access: Per-App VPN with GlobalProtect Guide
Are there performance considerations I should know about?
VPN performance depends on subnet sizes, tunnel count, CPU/memory on participating devices, and the encryption policy chosen. Monitor latency and throughput and adjust tunnel capacity as needed.
How do I rotate VPN certificates safely?
Plan a window for rotation, verify each side in a staging environment first, distribute new certificates, and perform a controlled cutover. Keep old certificates valid for a grace period to avoid outages.
What tools should I use for VPN troubleshooting?
AWS Console for VPN status, CloudWatch for metrics, VPC Flow Logs for traffic, and network analysis tools such as traceroute, ping, nslookup, and SSH-based device logs for on-prem devices.
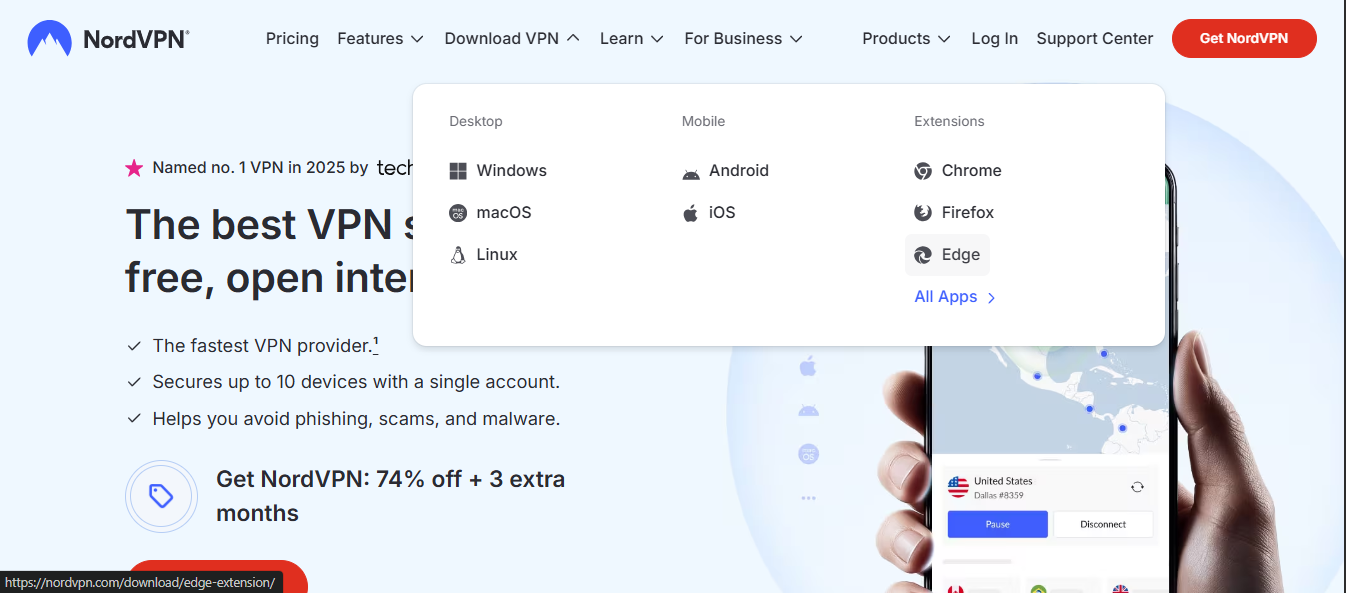
- NordVPN — aws vpn wont connect your step by step troubleshooting guide: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Sources:
科学上网 vpn:全面指南、评测与使用技巧,含常见问题与实用对比
Nordvpn Servers in Canada Your Ultimate Guide for 2026: Canada NordVPN Servers, Speed, Privacy, and Tips Las mejores vpn gratis para android tv box en 2026 guia completa y alternativas
极星vpn 完整指南:极星vpn 区域解锁、隐私保护、速度优化、设备支持与常见问题解析
Brave vpn kosten was du wirklich zahlen musst und ob es sich lohnt
Nordvpn extension for edge your quick guide to download install and use: A complete SEO friendly guide for Edge users