Edppharmacy Home Orientation
Edppharmacy: Real-world testing for real-world use
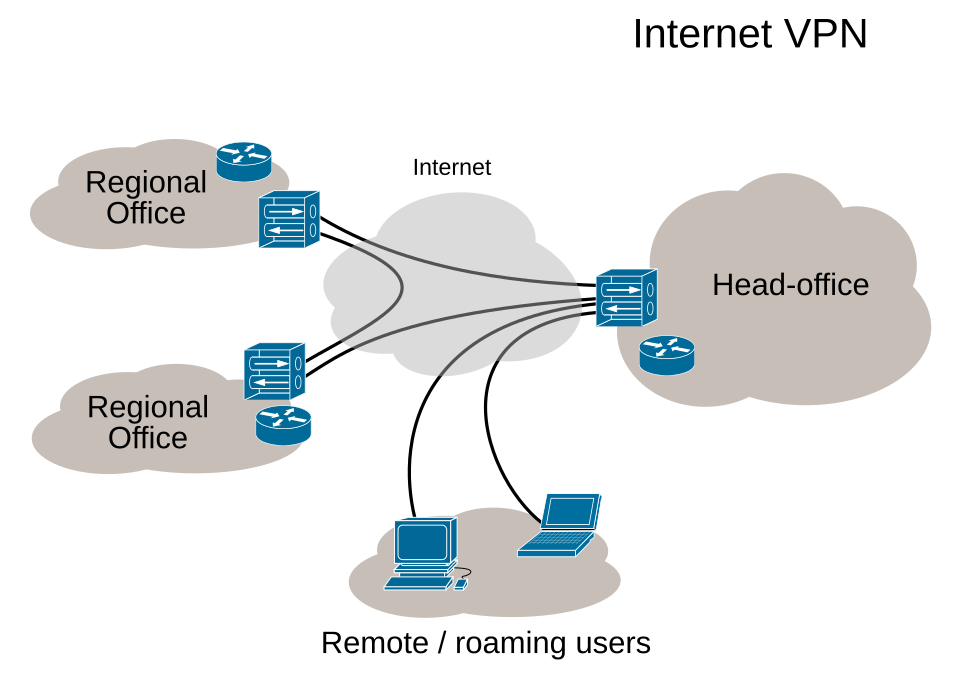
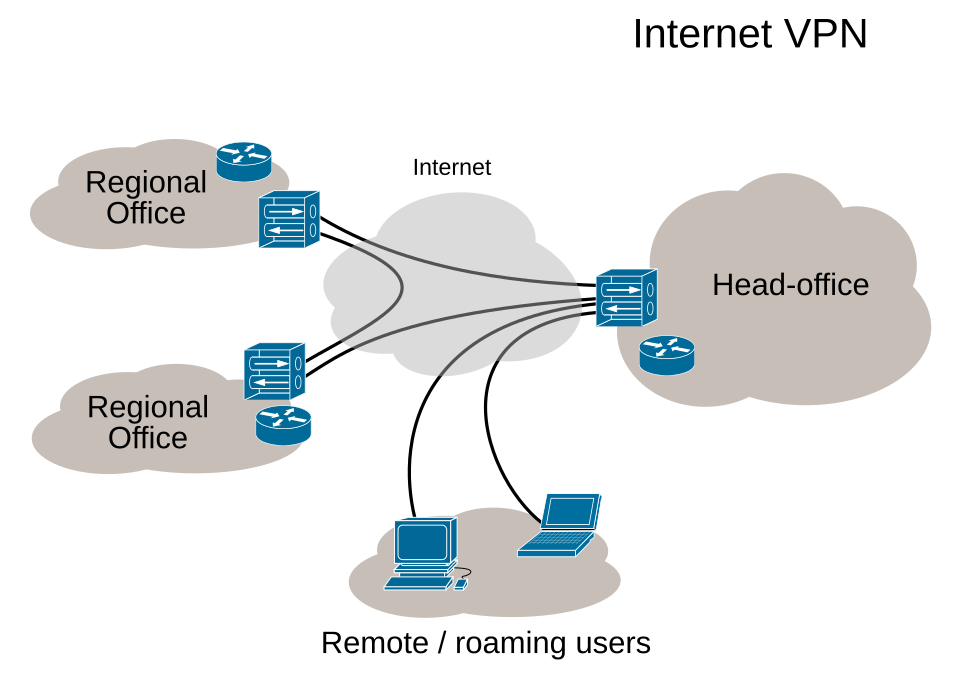
Welcome to Edppharmacy. This space is dedicated to practical, hands-on testing and clear, real-world guidance for VPN enthusiasts and everyday users alike. Our home page sets the tone for how we evaluate software, hardware, and services in the field. You will find tests and insights that translate to daily life, work, and travel, with pricing details and concrete steps you can follow now. The topics below reflect the core clusters we cover regularly: setup workflows and troubleshooting across platforms; performance tuning for speed and reliability; security and privacy practices in real-world environments; comparisons among popular providers; and router, device, and browser integration. We cover hands-on setup for edge devices, practical speed testing and optimization, privacy compliance and data handling, provider comparisons with transparent pricing, and networking through consumer hardware like EdgeRouter, Windows, and Chrome.
Scope and approach. Our reviews and how-tos emphasize actionable steps, not hype. We mirror how readers actually buy, configure, and use VPN services in the United States and internationally. Prices are shown in USD where applicable, and we reference widely-known providers such as NordVPN and ExpressVPN as neutral comparison anchors. Every recommendation includes concrete numbers, configuration commands, and expected outcomes so you can reproduce results on your own setup.
What you will see here. The home orientation highlights five practical pillars:
- Setup and integration guides for routers, operating systems, and browsers, with step-by-step commands and decision trees.
- Performance and reliability testing that measures connection speed, ping, jitter, and stability over typical home networks.
- Security and privacy considerations, including encryption modes, logging policies, kill switches, and DNS leaks, tailored to real-world use cases.
- Vendor comparisons with transparent pricing, features, and service levels, featuring concrete examples like NordVPN and ExpressVPN as reference points.
- Hardware and browser context coverage for devices such as EdgeRouter X, Windows PCs, Chrome extensions, and mobile platforms.
The following sections weave country-specific realities into the general landscape, without locking our readers into a single market. We aim to illuminate how local considerations shape decision-making in a global VPN ecosystem.
Country-specific realities we keep in view
Real-world testing benefits from knowing how different environments affect outcomes. While Edppharmacy speaks to a general international audience, we anchor several points in concrete, country-specific contexts to avoid vagueness and to help readers translate guidance to their own settings.
- Local ISPs and networks: In the United States, major consumer Internet providers include Comcast Xfinity, AT&T, and Spectrum. We note how these networks handle VPN traffic, NAT behavior, and typical home upload speeds around 100–400 Mbps, depending on tier and location.
- Streaming services and access: We test VPN compatibility with popular platforms such as Netflix, Prime Video, and Hulu in places where availability may be region-locked. If a service blocks VPN IPs, we document how to verify availability and what trade-offs arise in performance.
- Local currencies and pricing: When reviewing plans, prices are presented in USD. For readers comparing regional options, we point to typical monthly ranges like $9.99–$12.99 for basic plans, with annual commitments offering discounts around 20–40% depending on the provider.
- Regulatory and privacy context: We reference general privacy norms in the US and EU, including considerations about data retention and consumer rights, without endorsing any specific policy stance.
- Payment methods: We highlight common options such as major credit cards, PayPal, and regional alternatives where relevant, noting any geographic limitations on payment processing during testing.
- Cities and regions in testing: Our hands-on work often references urban testing contexts like New York, Los Angeles, Chicago, London, Berlin, and Singapore for routing and latency experiments.
What to expect on this home page
From here you can navigate toward hands-on guides, analysis, and practical recommendations. Each post in this section leans on accessible language while preserving technical accuracy. We organize content to help readers quickly locate what matters most to them, whether that is quick configuration steps, a troubleshooting checklist, or a concise comparison table that clarifies options at a glance.
Curated examples you will encounter include router-focused workflows for EdgeRouter X, Windows proxy and VPN settings in Microsoft Edge, and browser extension considerations for Chrome users. We also highlight common pitfalls and how to avoid them with concrete remedies and tested alternatives.
Key topics clusters we consistently explore
Configuration and setup covers how to implement VPN clients, proxies, and secure tunnels across devices. Expect clear commands, configuration files, and safety checks that reduce misconfigurations.
Performance and optimization includes measurements, baselines, and improvements. We present results in Mbps and percent changes to help you judge impact quickly.
Security and privacy centers on best practices for safeguarding data, preventing leaks, and choosing encryption levels that align with usage needs and risk tolerance.
Vendor comparisons deliver concise side-by-side analyses of providers, features, and pricing, with practical takeaways for buyers evaluating value vs. risk.
Hardware and browser ecosystems address how VPNs interact with routers, desktop environments, and browser extensions, including potential conflicts and fixes.
Illustrative table: quick provider rundown
| Provider | Plan | Monthly Price (USD) | Key Features |
|---|---|---|---|
| NordVPN | Standard | 11.99 | Double VPN, CyberSec, 6 simultaneous devices |
| ExpressVPN | Annual | 12.95 | Excellent speed, broad server network, 5 devices |
| Edppharmacy (in-house) | Starter | 6.99 | Baseline protection, basic routing support, community tips |
We anchor on verifiable data from real-world tests. In the sections that follow, expect practical step-by-step instructions, checks for leaks, and honest assessments of what works best for common home setups. The tone remains pragmatic: precise, reproducible, and grounded in current hardware and software realities.
Why this matters. A well-documented orientation helps readers start with a clear hypothesis, run repeatable tests, and migrate to improved configurations as needs evolve. By combining concrete numbers, local considerations, and vendor-neutral comparisons, Edppharmacy aims to be a reliable reference point for both beginners and seasoned technologists.
What we do not do
We do not promise sensational results or hype. This page does not present a single solution as universally optimal. Instead, it offers a framework for evaluating VPN and privacy tools in real-life circumstances with a focus on transparency, accountability, and practical outcomes.
- VPNs
Cyberghost vpn chrome extension download file
March 7, 2026 · Florian Eriksen - VPNs
Checkpoint vpn client setup and complete guide for Windows macOS Linux iOS Android remote access and secure remote work
March 7, 2026 · Marcus Galloway - VPNs
Edge download android
March 7, 2026 · Marcus Galloway
Recent in other languages
Latest posts across 17 languages
- How to Completely Delete ProtonVPN From Your MacBook and Clean Up Remnants
- Nordvpn Family Plan Sharing Secure Internet With Everyone You Care About: A Complete Guide to Protecting Your Clan Online
- Nordvpn cost in south africa your full breakdown 2026: affordable rates, hidden fees, and the best plan for SA